Cryptocurrency Wallets Defined: Types, Performance & Security
Cold wallets significantly scale back the risk of unauthorized access or hacking attempts by preserving sensitive data isolated from the web. Their offline nature creates a formidable barrier towards https://utilizewindows.com/crypto-wallets-for-brokers-full-guide/ remote exploitation. Wallets themselves typically don’t charge charges, but blockchain networks usually require a transaction fee (like gasoline fees) when sending crypto. As A End Result Of of this, we continued with our personal analysis, contemplating each company’s community and app security, authentication choices, code audits, certifications and extra. Tangem Pockets stands out as a outcome of its credit score card-sized, NFC-powered hardware that doesn’t require a battery or cables.
Custodial Wallets

No BitGo communication is intended to indicate that any digital asset companies are low-risk or risk-free. BitGo is not a registered broker-dealer and isn’t a member of the Securities Investor Protection Corporation (“SIPC”) or the Financial Trade Regulatory Authority (“FINRA”). Digital property held in custody aren’t assured by BitGo and aren’t topic to the insurance coverage protections of the Federal Deposit Insurance Coverage Corporation (“FDIC”) or SIPC.
Crypto wallets offer a method to handle and control your digital belongings directly, without relying on third events. Good wallets strike a steadiness between ease of use, self-custody, and safety. If you resolve to use a cold wallet, the first step is choosing the proper tool. The most common are hardware wallets like the Ledger Nano collection or Trezor. Their security has been examined by many users, making them appropriate for both novices and long-term holders. All The Time buy from official channels to avoid tampered counterfeit gadgets.
Security
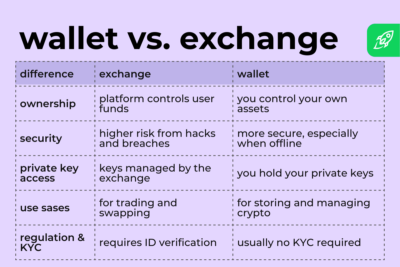
What they maintain are the digital codes often recognized as “keys” that grant entry to your crypto on the blockchain, a kind of ledger that features as an internet report of transactions. This article will break down the core ideas, examine key options, and information you on selecting the right solution in your wants. By the tip, you’ll grasp when to maintain assets on an change, when to maneuver them into a devoted wallet, and tips on how to defend your funds in opposition to frequent threats. You need a wallet that makes it simple to ship, receive, and manage your assets. Self-custody is the core precept of “not your keys, not your coins“.
A Letter From Mike Belshe, Bitgo Ceo And Co-founder
- All cryptocurrency transactions, once submitted to the blockchain, are ultimate and irreversible.
- While no technique is 100% foolproof, hardware wallets present a robust stability of safety and usefulness, making them perfect for storing massive quantities of crypto or long-term holdings.
- Crypto wallets additionally are available a quantity of totally different varieties, like software program and hardware wallets.
- Never take a photo of the recovery phrase, never retailer it in your phone album, e-mail, or cloud storage, as a end result of if these accounts are leaked, hackers can easily access your assets.
- Allocate solely what you need for daily operations to sizzling wallets, maybe with a small buffer, while keeping long-term holdings and significant assets in chilly storage.
- Understanding how each software works is crucial for managing risk and staying in management of your digital belongings.
Common unsecured creditors are decrease in priority on the record of creditors in a chapter continuing. So, you’ll be able to have a noncustodial software program sizzling wallet, a noncustodial hardware chilly or sizzling pockets, or a custodial hardware cold pockets. These are the most typical sorts, however you may also encounter different combos.
Digital belongings seem like the investment of selection for Gen Z, who are 4 instances extra more likely to personal a cryptocurrency than they are to have a retirement account. Collectively, these keys allow you to ship and obtain crypto with out compromising the integrity of the transaction. The public key’s visible to others, whereas the non-public key proves your possession. As Soon As both are verified, the steadiness in your crypto pockets will increase or decreases accordingly. Whereas there are important safety concerns for both software program and hardware wallets, new solutions have begun to emerge that purpose to integrate the best options of each.
You’re Just 60 Seconds Away From The Most Effective Privateness Online
For example, in case you are bodily compelled to reveal your recovery phrase, you can hand over the model with out the passphrase, which holds solely a small quantity. The massive holdings stay hidden in the model that requires the extra passphrase. For example, in 2017, somebody photographed their recovery phrase and stored it in e mail. Hackers obtained in and stole lots of of thousands of dollars’ value of Bitcoin. Initiating the transfer from the trade requires deciding on the specified cryptocurrency and specifying the recipient’s wallet address.